Office 2016 With Product Keys Professional Plus Crack Latest

Office 2016 Product Keys is an integrated suite of productivity programs that provides modern offices with everything they need to create and manage documents and other office-related tasks, from organizing information to writing documents and updating databases. When installing it on your computer, the installation wizard offers options that let you choose between several applications bundled together – no other package offers such comprehensive coverage! Office 2016 Professional Plus IMG and ISO files required for running offline installers are freely downloadable for all versions of Windows 10. Once released, you can download this latest version of Office for Windows 10.
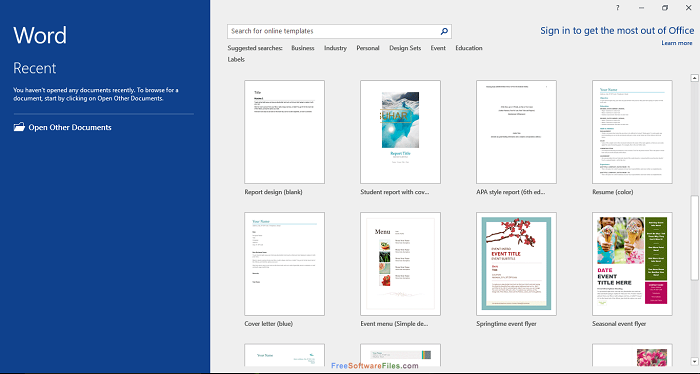
Office 2016 Professional Plus Crack Product Key for both 64-bit and 32-bit Windows is a productivity suite, featuring applications tailored specifically to the needs of office and document administrators. All these programs can be found within one convenient package – Microsoft Office 2016. Document Studio comes packed with features designed to assist with creating and organizing documents, spreadsheets, presentations, and databases. When installed onto your computer, you are given the choice to customize its look according to your preference – not many other programs provide such an impressive array of programs in a simple package that makes setup effortless.
Free Microsoft Office Professional Plus 2016 Product Key
Microsoft Cracked has long been recognized as providing an ideal office solution to both home and workplace users alike. Microsoft Office 2016 Professional Plus Crack Lifetime activator stands out as an exceptional option on the market, with all of the tools necessary for creating, editing, managing, presenting, and analyzing records, data sources, demonstrations, and spreadsheets. In its Nov 2017 release version, it also comes equipped with MS Project to handle project-related documents as well as MS Visio which can handle blueprints such as flowcharts. Plus its easy user interface improves efficiency! You can also download Microsoft Office 2013.
Before installing Office 2016 Cracked here, it is necessary to prepare your computer. As it is advisable to only have one Office installed at any given time, uninstall all previous Office versions from your system – including old Office versions, Office 365 subscription versions, or trial versions of Microsoft 365 trial accounts. Option 2 provides the best method for uninstalling all Office programs by completely using their uninstallation support tool of Microsoft’s uninstallation guide or their removal tool called Microsoft Support and Recovery Assistant; click here to directly download it now.
Microsoft Office 2016 Product Keys FREE Active lifetime
MS Word is an efficient solution for creating, editing, and formatting records as well as styling records. Succeed provides Excel spreadsheet support with statistical computation capabilities. Furthermore, PowerPoint enables eye-catching demonstrations by providing options to alter both style and structure of slides. Outlook provides the capability of sending and receiving e-mails; in short, it’s an efficient office suite for creating, editing, and managing records.
Microsoft’s Productivity Suite, known as Office 2016 Professional Plus Activation Key, has made significant advances with this release. Notable upgrades to the user interface and components have been moved up a level for an enhanced professional workspace experience. Word, Project 2016, PowerPoint, Visio, outlook OneNote, and Excel all form part of this incredible suite; simple file-sharing features have also been implemented along with enhanced look-and-feel improvements and grammar fixes making “Microsoft Office 2016 Professional Plus Product Key” truly epic!
Office 2016 Professional Plus Product Key Free {100 % Working}
Office enthusiasts had long anticipated Office 2016 Professional Plus’ release and its many enhancements; mathematics input can come in handy when adding equations in Excel, Word, or PowerPoint; timeline preview has also been greatly enhanced with multiple instances available; while another key feature includes Higher DPI inclusion for making documents look even clearer on higher screen resolutions.
Key Features:
- Create, edit, open, and save files directly in the cloud;
- New search tool for commands named “Tell Me” in Word, PowerPoint, Excel, and Outlook;
- Word and PowerPoint offer additional “Send As” options;
- Co-authoring in real-time with other Office 2016 Professional Plus Permanent Activation Free Online users.
- Easy file sharing. ameliorated user interface and products.
- Addition of new themes. Easier formatting process. Improved and faster grammar checker in comparison with previous releases.
- Increased DPI support of up to 300% allows your documents to appear clearer.
- Catchy Themes.
- The user interface should be intuitive and simple for maximum efficiency.
- Ribbon-based user interface.
- Create stunning presentations using powerful word processors
- Add media files to documents and presentations
- Customize the layout and style of documents
- Create and edit spreadsheets containing mathematical calculations
- Outlook 2016 allows for easier email management.
- Document project documentation.
- Create and Edit Flowcharts and Other Diagrams
- Many other powerful features and options exist as well.
Technical Details:
- Software Category: Office 2016 Professional Plus Product Key Activator Tools.
- Developer’s Website: Microsoft Office 16 Official Website.
- version of Free Trail and Setup Size is 2.53GB each; available for download: Yes
- Compatible with Windows 8, Windows 7, and Windows 10.
Office 2016 Professional Product Keys
- 3KT0I-DJBRD-0RY44-N33RJ-HOTXO
- 4XHRA-S833P-11XJ1-M7OWF-KPGN4
- LY030-JCSWR-TT0P7-3JJH5-3E3L3
- G0XLG-FEI7E-U0030-72YD4-OR0Q4
Office 2016 Professional License Keys
- OQ1J5-ZV0P2-28FSZ-P6MYW-VY7LL
- 92CFI-VEDTD-PSJ57-GDYJP-4F0CG
- 6WC03-CH94K-SYZY3-5TGX0-23WXF
- ES6F5-CWG2A-BDR13-6BTV0-SO97F
Office 2016 Professional Activation Keys
- G8RYD-KO63K-POV2G-0SY02-Y1NBB
- XGQP7-47C0S-4PFYQ-VY4E2-9VD8T
- 9K3R8-6OBB5-J9PPA-PGELW-COHSQ
- IF4PU-QF091-UFR80-2ESSV-QNMRQ
Office 2016 Professional Registration Keys
- NXA6J-E4T1Q-TZWDW-EPQ9R-KDML
- YUJC2-PJPLY-MQU5N-V0NPR-IQ8OH
- AHKL5-S85BO-P48K4-JV379-17X3H
- ZTEZZ-YCLET-QMPBQ-P2A6V-ELE4F
Office 2016 Professional Serial Keys
- OC2FJ-GNSAZ-1B68E-F907V-RUQ5T
- RW067-Z4K69-FR43M-GB4NO-U9LHO
- GXQKI-5ZTE3-AEPTD-NL6NQ-JBWEK
- G9GUY-GT0QK-JOE2E-V5T61-2J8I6
Office 2016 Professional Code 2023
- B48GW-1HF6K-CKRHW-UZX7C-0J7EM
- D18AP-DCGM7-DCW6C-QYQ7F-G9YXX
- ACQP-F5U3O-7PZYO-BS30R-L2AUA
- Z0OHT-MR4XW-76VTB-K46UN-ON7SQ
System Requirements:
- Computer with a processor that operates at 1 gigahertz or higher and supports SSE2.
- Memory (RAM) of 1 GB 32 bit; and 2 GB 64 bit).
- Hard Disk Space Available
- To take full advantage of display graphics hardware acceleration requires a DirectX10 graphics card with 1024 x 576 resolution and 1024x 576 screen size.
How To Install?
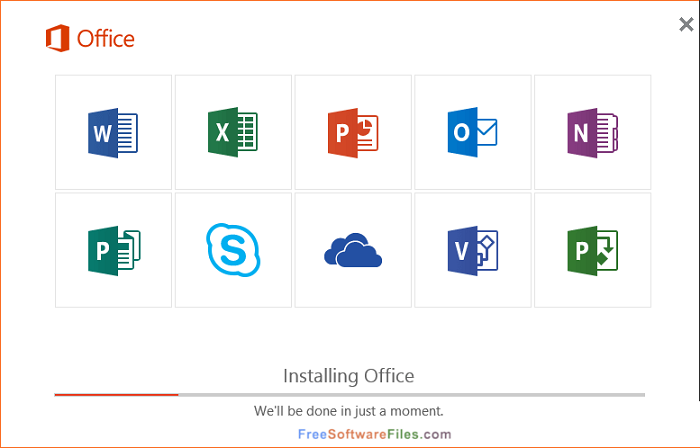
- Once complete, on the left-hand side of this same window you should see that an Office device appears under This PC.
- To install Office 2016 Professional Plus, right-click on this new device (1), select its content from the right side, double-click its setup file (2 in this image) to begin the installation process, and double-click again on its setup file (3).
- This will start the installation process.
- Installer will select the optimal version for your computer.
- however, if you need the 64-bit installation option instead, accessing your Office folder and running Setup64 directly can force its installation.